Today drones are flown in many types of assets ranging from sewer systems to production units in refineries. For many pilots, the privacy of their data is of paramount importance. Whether it’s a matter of intellectual property or the sensitivity of the asset from a national security perspective, it is always essential for the data gathered by operators to be secure.
The level of data security built into our products is important to some users and we understand that transparency is key. Here is an overview of all the measures we are implementing to preserve the integrity of your data.
IT Security is built in the core of our drones
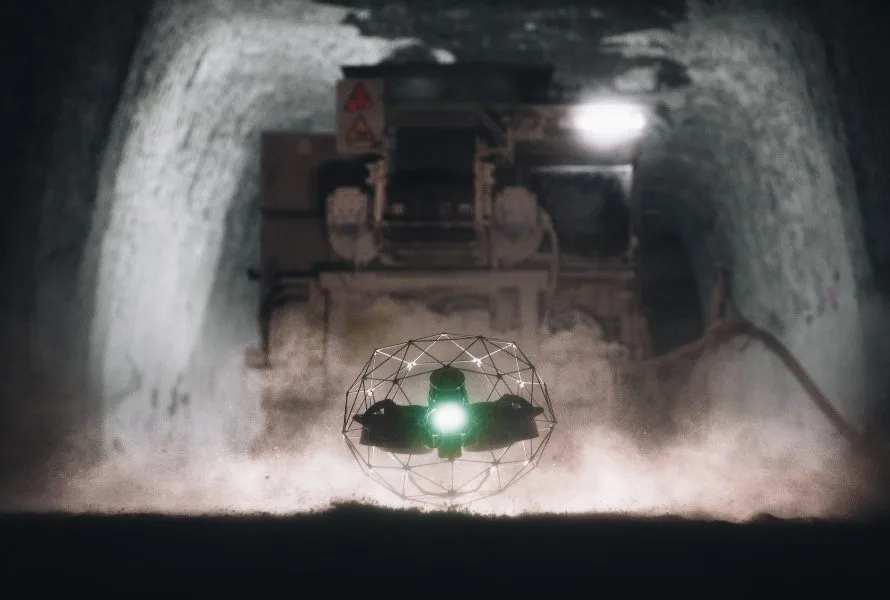
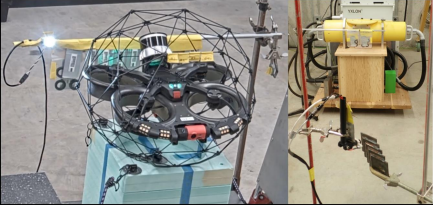
Since the release of our first product Elios 1, we are working with companies operating some of the most critical assets when it comes to national security. More than half of the nuclear plants in the United States are using our technology to prevent human exposure to radioactive and dangerous areas. We also work with some of the largest industrial groups in the world where assets are often full of intellectual properties that require the highest degree of confidentiality in data management. Because of this, we embed robust IT security measures in the core design of our drones.
Designed to fly in signal-deprived environments
Our technologies are designed for indoor uses in signal-deprived environments. They were engineered in a way where the entirety of their operations could be performed with no external signal reception, be it GPS or internet. This means that the only device connected to the drone is the Ground Control System (GCS). This requirement of flying indoors means that the drone is engineered at its core to operate in absence of any external connection, making it inherently safe from a data security standpoint.

Safe data management
The data gathered by the drone is stored on SD cards on the drone. Operators have the option to save a screen-recording on the tablet as a back-up. These are the only two places where the data is stored; at no point is it stored online. Operators can remove the SD cards after the flight to upload them to their computer. Neither the drone nor the GCS needs to be connected to anything else but each other while the UAS (Unmanned Aerial System) is in use. No components of our UAS ever need to be connected to the internet, as updates can be done offline. The tablet, which is the only part which even has the option to connect to the internet, can have its connection permanently blocked before it leaves our production facility.

External components
The only components which are not proprietary are the cameras and the transmission system. Both the Elios 1 and the Elios 2 are equipped with a DJI Lightbridge 2 radio link. The Ground Control System (GCS), is composed of a DJI controller and a Samsung tablet. The Cockpit app, which is installed on each GCS, communicates with the transmission system of the controller through an SDK provided by DJI. In order to activate the DJI SDK, a one-time internet connection is required to exchange a token with DJI’s IT infrastructure. This operation is part of our production process and is done during the post-production test performed at the end of the process. After this, neither the Cockpit app, the controller, nor the Elios 1 or Elios 2 drones ever need to communicate with any of DJI’s IT infrastructure again.
Proprietary components
From the design of the drone and its parts, to the firmware on the drone, to the app on the tablet, to the software on the computer, we design everything in-house from the ground up. We are in charge of every component on our drones. There is no communication between our systems and third-parties; the data gathered with our technology remains solely with the operator.
Link between the Ground Control System and the UAV
The GCS is composed of a Lightbridge 2 controller and a Samsung tablet. The uplink from the GCS is encrypted so that it is virtually impossible for an external source to take control of the drone. The downlink is not encrypted, but the receiver must be paired to the UAV to access it. The pairing can only be done by connecting a mobile phone or a tablet (not the GCS tablet), which has DJI Go to the GCS and manually launching the pairing on the drone. Connecting to the downlink without a paired GCS is a very complex process that could only happen if an expert were to steal the information of the drone by taking the hardware and reading its information, and code a sniffer device to access the downlink, all while being in range of the UAV.
The tablet
The tablet is the only device in our UAS that can be connected to the internet. This only happens if the operator connects to a WiFi. As mentioned above, we furthermore offer the option to completely and permanently disable the tablet’s access to the internet, in which case all updates must be done offline (more about this below).
The tablet is shipped with Cockpit installed. Cockpit updates or installations will automatically fail in the installation process in case of middle-man attacks.
The tablet connects to the GCU with a USB-C cable. In the event where the tablet connects to the internet, the Cockpit app does not share data with third-parties. However, users have the option to save to the device screen-recordings of the Cockpit app during flights as a backup should the drone be lost or damaged in-flight. In this case, if your tablet is hacked while it is connected to the internet your device screen-recording may be exposed to a security breach. As such, if you want to ensure the highest level of security, we recommend to permanently disable the tablet’s access to the internet.
Offline drone management & updating
Whether the tablet’s connectivity is permanently disabled, or whether the tablet has simply never been connected to a WiFi, the entire UAS can be operated without ever having been connected to the internet. In these cases, updates must be done offline. For the Cockpit app, operators need to download our APK available to our clients on our server and update the app on a computer. In case of doubts, operators can run a checksum on the APK to ensure the file’s integrity. For the drone firmware, it can be downloaded from our servers and installed on the drone with an SD card. Our software and firmware are only distributed on our servers and are available nowhere else. In case of doubts, operators can contact Flyability directly. If necessary, Flyability can ship SD cards with the latest firmware version. Updates are coded and compiled in-house and do not involve third-parties in any way.
Best practices
There are also a few steps which can be taken by the operator to enhance data safety. First, the drone and the GCS should be kept safe when on site. This can be done by keeping the SD cards out of the drone and on your person, as well as keeping the hardware locked with a padlock in a transportation box. We recommend deleting all data from the Camera and the Log SD cards after downloading them to your computer. Once the data is securely downloaded, we also recommend deleting the backup footage on the tablet if this option was enabled. Finally, we recommend keeping the transportation box locked at all times with a padlock when stored.
For inspection service providers, we recommend entering client assets with empty SD cards and immediately uploading the data from the drone after the mission. This allows the operator to delete data from SD cards and tablet backup so as to leave the site with no data from the client.
For operators working in public safety, the drone can be flown with no SD cards in order to have all the data on the tablet backup in the hands of the operator, should the drone be destroyed or taken while in mission.
Data collected by Flyability
Flyability only collects data in one instance: when the drone is armed while the tablet on the GCS is connected to the internet. In these cases, we collect the unit ID, which is encrypted and can only be read by Flyability, the time of flight, and the firmware version. Owners are notified of this and have the option to opt-out.
Operators also have the option to send logs to Flyability in cases where debugging is needed, although this is by no means mandatory for debugging to be done.
Check our User Manual for more information. Details are available in the About Panel chapter and the Privacy Settings chapter.
Working together to enable safer, faster, and cost effective inspections
We thrive to provide our clients with everything they need to adopt and scale in the use of our technology. We actively work with clients’ IT departments to overcome any hesitations. Please let us know if you need support or information.